Quantum Computing Threat Timeline: When Does It Actually Become a Real Risk for Crypto?
Crypto loves doom charts. Quantum is the ultimate one because it’s vague enough to be scary, technical enough to be hard to argue with, and far enough away that nobody has to do anything today.
Migration takes forever, and “Q-Day” doesn’t need to be tomorrow to wreck you.
Cryptanalytic quantum capability is still 5–15 years away for mainstream crypto targets, but signature migration for Bitcoin/Ethereum class networks is a 6–10 year coordination problem.
That mismatch is where the risk becomes material.
What Quantum Actually Breaks
Quantum computers don’t magically break all cryptography.
They mainly threaten two families of math:
Integer factorization → breaks RSA
Discrete logarithms → breaks elliptic curve cryptography (ECC)
That second one is the big one for crypto. Bitcoin, Ethereum, Solana, Monero, Polkadot, basically everything:
– ECDSA (secp256k1)
– Ed25519 / EdDSA
– BLS signatures
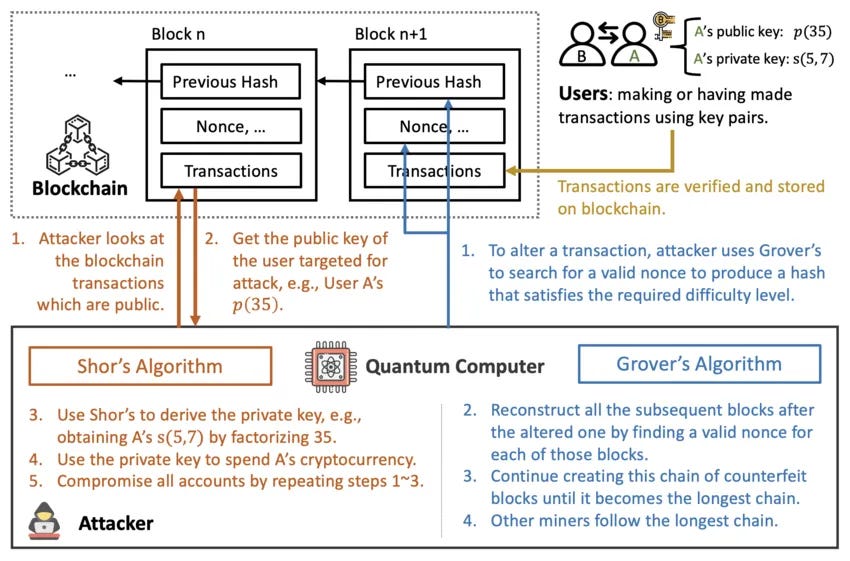
All live in the elliptic curve world. Shor’s algorithm lets a sufficiently powerful quantum computer solve those problems in polynomial time.
If a quantum computer gets big enough, it can derive your private key from your public key.
Meanwhile, hash functions (SHA-256, Keccak, SHA-3, etc.) only get a square-root speedup via Grover’s algorithm.
256-bit → effectively ~128-bit security.
128-bit is still absurdly strong. So the Achilles’ heel is public-key signatures, not hashing, Merkle trees, or PoW itself.
Q-Day vs migration clock
There are two clocks running in parallel:
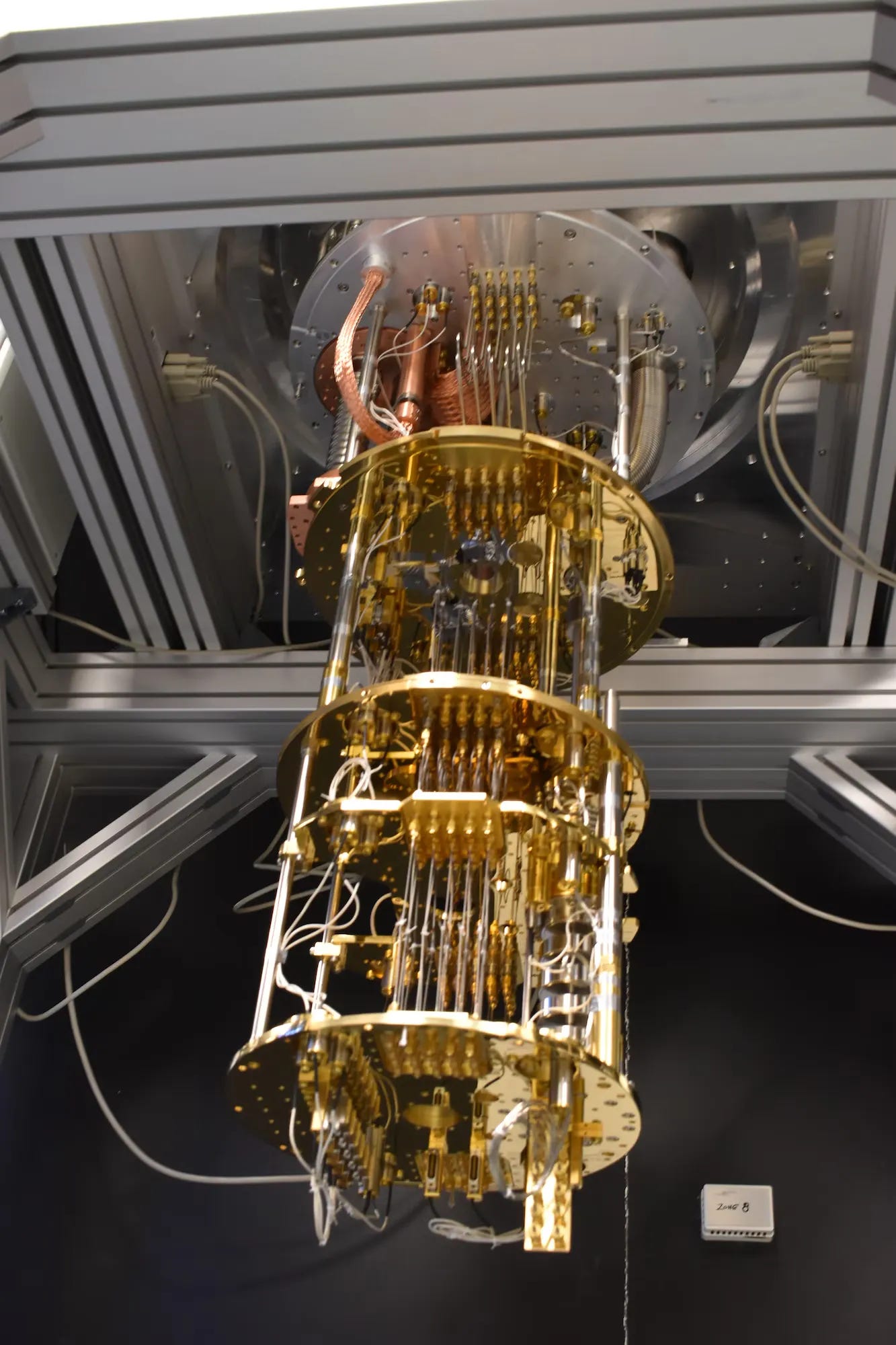
– Quantum progress clock: how fast we get from “cool lab demo” to a cryptographically relevant quantum computer (CRQC).
– Crypto migration clock: how long it takes to get real networks to move from ECC signatures to post-quantum signatures (PQC) without blowing up UX, infra, wallets, exchanges, smart contracts, custody, and governance.
Institutions are already treating quantum as a disclosed risk. BlackRock literally added quantum risk language to a Bitcoin ETF prospectus.
When does it become real for crypto?
Near term (2 years)
No one is cracking secp256k1 or Ed25519 in the next two years.
We’ve seen 24 logical qubits so far, while ECC-256 attacks need tens of thousands of physical qubits, and the gap in runtime and error rates is still huge.
In this phase:
– PQC standards are here. NIST finalized ML-KEM, ML-DSA, SLH-DSA
– Policy timelines are firming up. NSA CNSA 2.0 points federal systems toward PQC migration with a long runway and a 2035 end state.
– Crypto teams start prototyping instead of hand-waving. Ethereum has L2 testing in the plan, Bitcoin devs exploring soft-fork paths.
Real risk is that if a chain waits until 2030 to start serious work, it’s basically speedrunning a governance crisis later.
Mid term (5 years)
This is where things start to matter operationally, even if Q-Day is still ahead.
Expectations like 50–100 logical qubits in this window, improving error correction (LDPC), and longer continuous runtimes.
Even if those numbers don’t break crypto directly, they tighten the confidence interval, and markets hate uncertainty.
This is also the window where migrations begin:
– Bitcoin likely needs a soft fork introducing PQC support / dual signature era around 2028–2030. – Ethereum likely pushes PQC testing on rollups first, then validator credential migration, then EOA and smart contract touchpoints.
If ecosystems can’t coordinate wallets, exchanges, custody, infra, and apps, you get a long messy gray zone where a meaningful chunk of assets are sitting in legacy schemes.
Long term (5–15 years)
This is the phase where the threat becomes material in the way people mean it.
For ECC-256 (Bitcoin/Ethereum ECDSA):
→ ~2,871 logical qubits (optimized) and ~34K physical at a 12:1 ratio (plus big gate depth / runtime constraints).
If we ever see logical qubits >500 and error rates <10^-10 together, treat it as the threat regime shifting upward.
Attacks that aren’t theoretical in this phase. Stolen coins from old exposed-key addresses. Weird dormant stashes moving.
What’s actually vulnerable (and what isn’t)
The real Achilles’ heel is public-key signatures (Shor). Shor’s algorithm becomes practical on a CRQC, it targets discrete log / factoring hardness. That means:
– ECDSA / sep256k1 (Bitcoin, Ethereum EOAs) is critical risk
– Ed25519 / EdDSA (Monero, Solana, Polkadot, etc.) is also critical risk
– BLS (Ethereum consensus validators) is critical risk, with extra chain-safety implications
– RSA matters mostly for broader internet/custody infrastructure
Parts of crypto not meaningfully threatened.
Encoding schemes, smart contract logic (non-crypto), and consensus rules aside from keys are not magically undone by quantum. The main issue is the signature layer and any key exchange relying on ECC.
SHA-256 goes from 256-bit preimage security to ~128-bit effective security under ideal Grover assumptions, which is still chunky.
Also, PoW mining doesn’t get hacked by Grover in a clean way. If someone got a speed advantage, difficulty adjusts, and it becomes an economics / detection game.
Zero-knowledge privacy doesn’t get retroactively revealed by quantum alone because there’s no encrypted secret embedded to later extract. The threat is fake proofs once quantum exists.
Bitcoin and Ethereum where quantum risk actually shows up
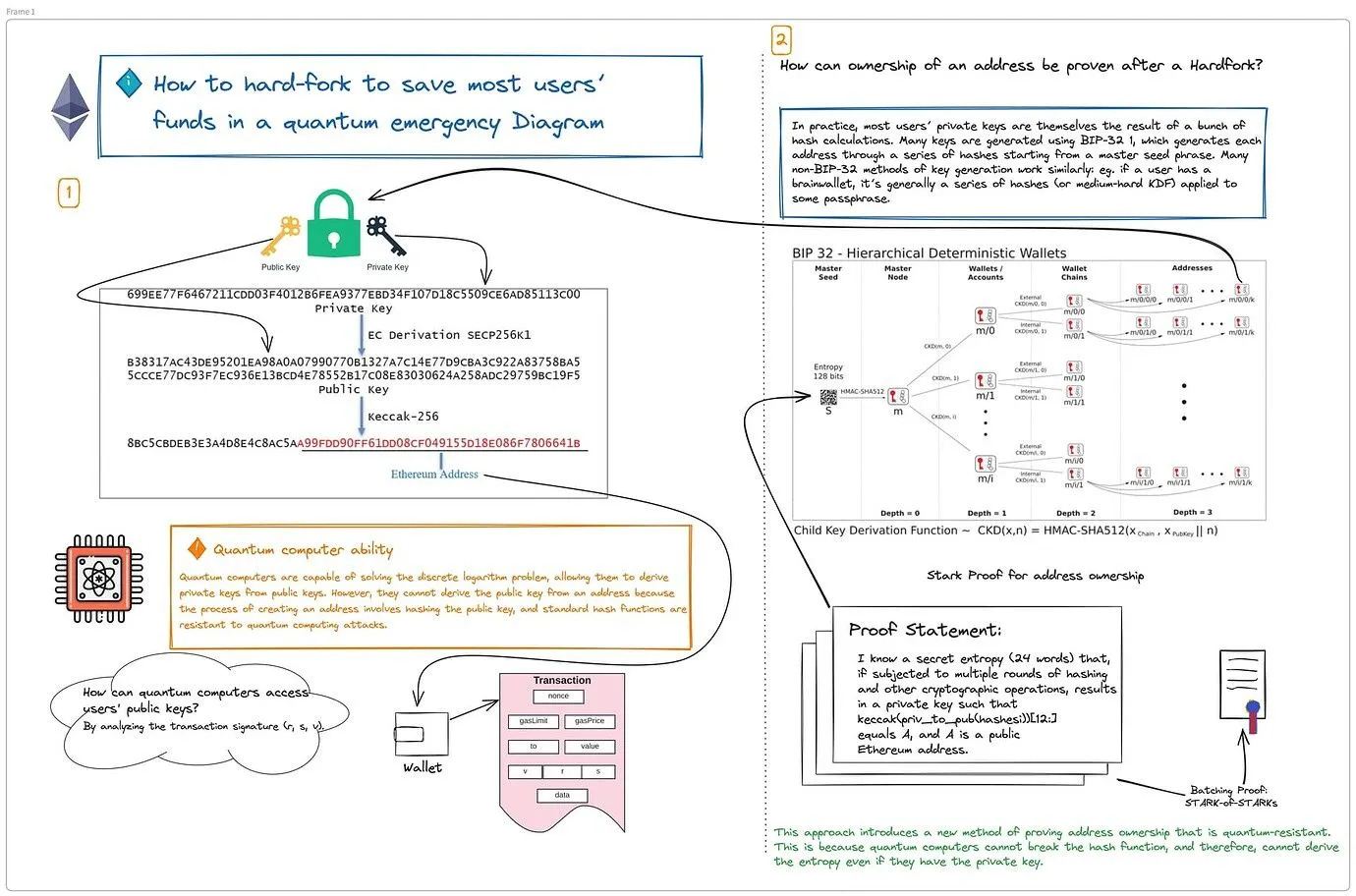
Bitcoin’s exposure mostly comes down to how addresses and scripts work. If a pubkey has never been revealed, P2PKH gives you some breathing room.
The address only shows a hash of the public key, and stealing those coins would still require an absurdly hard preimage attack, even with Grover-style speedups. So untouched, never-spent UTXOs are not first in line.
The problem is anything with an exposed pubkey.
→ Once you spend from an address, the pubkey is out in the open. If you leave funds there, those UTXOs become quantum-targetable later.
→ Same story for old P2PK outputs where coins were paid directly to a public key, including a big chunk of early-era BTC that’s been sitting untouched for years.
→ Taproot also exposes a 32-byte x-only pubkey in the output itself, which trades efficiency and flexibility for losing the hash-layer buffer.
~25–30% of BTC appear to have exposed pubkeys. About 3–5% comes specifically from P2PK outputs.
Ethereum has the same ECDSA problem at the account layer, plus an extra one at the consensus layer.
EOAs and many contract patterns rely on ECDSA-style assumptions. Validators rely on BLS12-381.
A validator key compromise is uniquely dangerous because it can enable fake attestations, slashing chaos, and in the worst case influence over finality.
Ethereum’s state is also fully scannable. If an attacker can derive keys, they can simply prioritize the richest accounts first.
On top of that, parts of the smart contract stack depend on signature recovery (like ecrecover), which would need to be updated or deprecated during a post-quantum transition.
The realistic mitigation path is staged. Test PQ signatures on L2s first, migrate validator credentials next, then handle EOAs and contract-level changes, and only later sunset ECDSA entirely.
What you can do today
Nfa, just operational hygiene.
If you’re a BTC user
– Avoid address reuse, keep pubkeys hidden as long as possible
– Be aware Taproot outputs expose pubkeys in the UTXO set (great tech, different risk profile)
If you’re an ETH user
– Know that every account that has sent txs has exposed pubkeys in signatures, and attackers can scan state for balances
– Watch the roadmap for when PQ signatures show up on rollups first
Closing thought
Crypto has survived exchange collapses, civil wars. hacks, forks, even nation-state attacks. If people treats quantum like an engineering problem, it’ll survive this too.